Real-Time eBPF Security Platform
FalconEye
Kernel-Level Threat
Detection for EKS
Detect container threats at the Linux kernel — before they ever reach a log pipeline. FalconEye deploys CNCF Falco’s eBPF engine across large-scale Amazon EKS clusters, delivering sub-second detection with minimal system overhead.
< 1s Detection
Kernel-level threat capture at the point of event generation. No log pipeline delay.
< 5% CPU Overhead
eBPF driver validated across 100+ node clusters under sustained high-throughput traffic.
100% AWS-Native
EventBridge, Security Hub, S3, CloudWatch. No self-managed middleware required.
Why Log-Based Security Breaks at Scale
As container environments grow to hundreds of nodes, traditional log-aggregation approaches hit hard limits in latency, cost, and detection effectiveness.
Detection Latency in Minutes, Not Seconds
Shipping all runtime events to a centralized Data Warehouse and searching by keywords means threats are identified minutes to hours after they occur — far too late for meaningful incident response.
Infrastructure Costs Spiral with Node Count
Large OpenSearch clusters, Kinesis streams, and massive S3 storage grow linearly with scale. At 100+ nodes, monitoring infrastructure can rival the cost of the workloads it protects.
Blind Spots Across Multi-Tenant Environments
MSPs managing dozens of client EKS clusters lack a unified, real-time view. Siloed log pipelines per tenant create operational overhead and security blind spots.
Log Search Only Finds What You Already Know
Keyword-based log queries can only find what they are told to look for. Kernel-level events like privilege escalation, container escape, and reverse shells require real-time syscall interception — not post-hoc search.
Security at the Speed of the Kernel
FalconEye shifts threat detection from the log layer to the kernel layer — catching threats at the moment they happen, not after they are written to a log.
Sub-Second Kernel Capture
Falco eBPF intercepts syscall events directly at the Linux kernel — process execution, file access, network connections, privilege escalation — before they ever reach a log pipeline.
Minimal Overhead at Massive Scale
No sidecars, no application instrumentation, no container restarts. eBPF operates transparently at the kernel level with near-zero impact on production workloads.
Serverless Event Routing
Actionable findings flow through EventBridge, Security Hub, S3, and CloudWatch. Only alerts are routed — not raw logs — dramatically reducing pipeline volume and cost.
From Kernel Event to Security Finding
A lightweight, event-driven pipeline that detects threats before they become log entries.
eBPF Capture
Falco eBPF DaemonSet intercepts syscall-level events on every EKS worker node at the kernel level.
Rule Evaluation
Pre-built Falco rulesets evaluate events in real-time: container escape, privilege escalation, file access, reverse shell.
Sidekick Routing
Falco Sidekick forwards matched findings to Amazon EventBridge for fan-out to downstream consumers.
Security Hub
Findings are normalized to ASFF format and aggregated in AWS Security Hub for unified visibility across clusters.
Dashboard & Archive
CloudWatch dashboards for real-time monitoring. S3 durable archival for audit trails and forensic analysis.
Large-Scale EKS Security Architecture
Purpose-built for MSPs and DNBs operating hundreds of EKS nodes across multiple clusters.
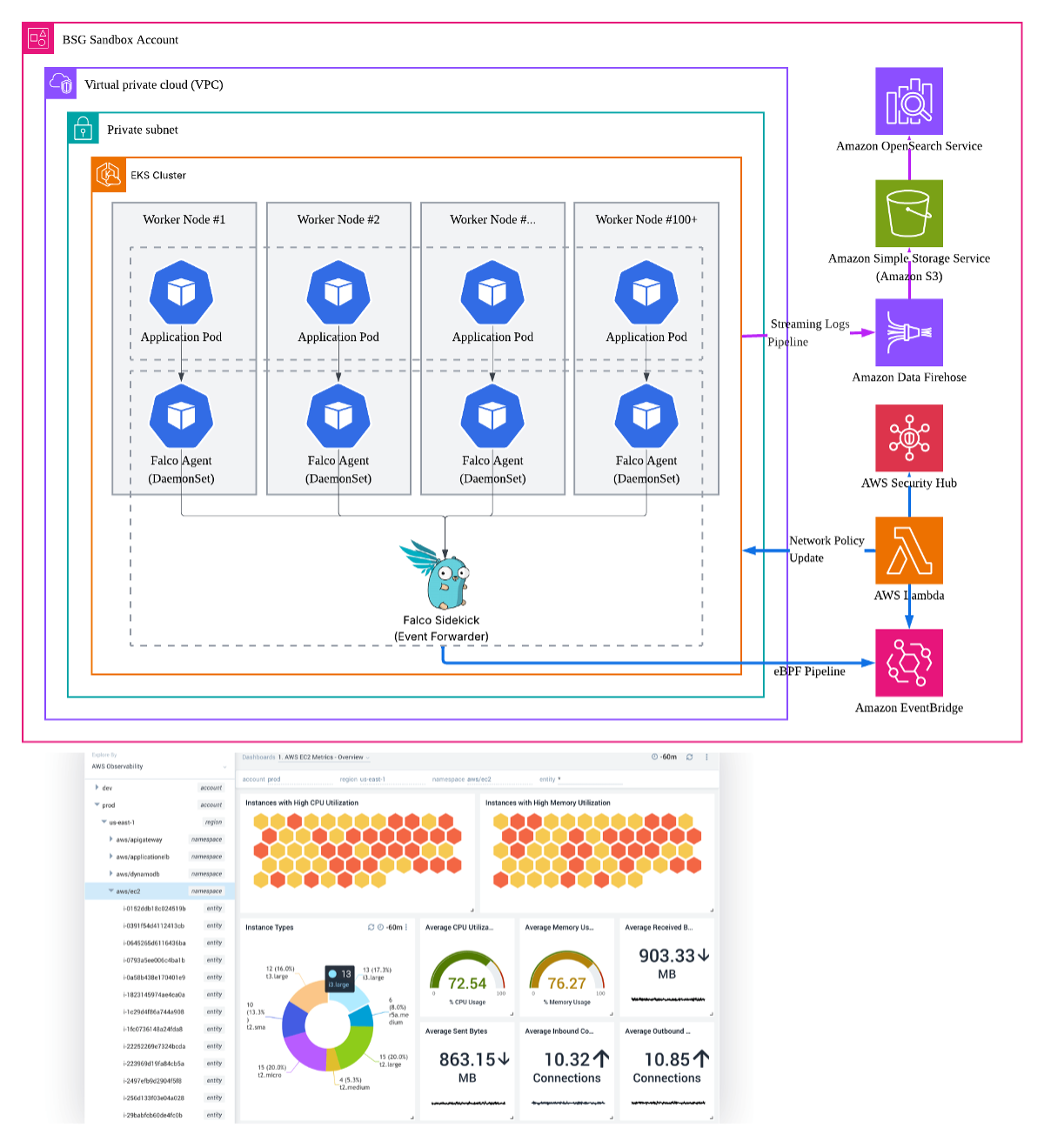
Kernel-Level eBPF Detection
eBPF engine deployed on every node for real-time syscall capture.
- Falco eBPF DaemonSet (Amazon Linux 2023)
- Kernel syscall interception (< 5% CPU)
- Pre-built + custom Falco rulesets
- Memory footprint < 512 MiB per node
AWS-Native Event Routing
Actionable findings only — no raw log shipping.
- Falco Sidekick → Amazon EventBridge
- AWS Security Hub (ASFF format)
- Amazon S3 (durable event archival)
- Amazon CloudWatch (operational dashboards)
OpenSearch Comparison Pipeline
Parallel log-based pipeline for quantitative performance validation.
- Amazon Kinesis Firehose (log ingestion)
- Amazon OpenSearch Service (keyword search)
- Identical threat scenarios on both pipelines
- Objective latency / throughput / resource metrics
Quantitative Proof: eBPF vs Log-Based Search
Under identical traffic conditions, FalconEye benchmarks real-time eBPF capture against traditional OpenSearch keyword search — producing objective, reproducible performance data.
| Metric | eBPF Pipeline | OpenSearch Pipeline |
|---|---|---|
| Detection Latency | Seconds (P95) | Minutes to Hours |
| CPU Overhead per Node | < 5% | Dedicated cluster required |
| Detection Method | Kernel syscall interception | Post-hoc keyword search |
| Infrastructure Footprint | DaemonSet only | OpenSearch + Kinesis + S3 |
| Scaling Model | Linear with nodes (lightweight) | Storage / compute heavy |
| Real-Time Capability | Yes — at event generation | No — after log ingestion |
“FalconEye doesn’t just claim eBPF is faster — it proves it. Every metric is measured under identical traffic loads, identical threat scenarios, and identical cluster configurations.”
Built for Scale-Critical Operations
Where real-time detection and lightweight overhead matter most.
Managed Service
Providers (MSPs)
- Centralized monitoring across all tenant EKS clusters
- Unified ruleset management from a single pane of glass
- Add tenants without adding monitoring infrastructure
- Real-time visibility without per-tenant log pipelines
Digital Native
Businesses (DNBs)
- Hundreds of nodes generating millions of events per hour
- Lightweight alternative to heavy Data Warehouse approaches
- Zero application impact — no sidecars, no code changes
- Cost-efficient security that scales with business growth
Regulated
Enterprises
- Pre-built Falco rulesets aligned to ISMS-P control items
- Continuous runtime monitoring for compliance evidence
- Automated evidence collection for audit readiness
- Financial, healthcare, and enterprise sector coverage
Ready to See eBPF
Detection in Action?
Deploy FalconEye on your EKS clusters and experience sub-second threat detection at the kernel level.